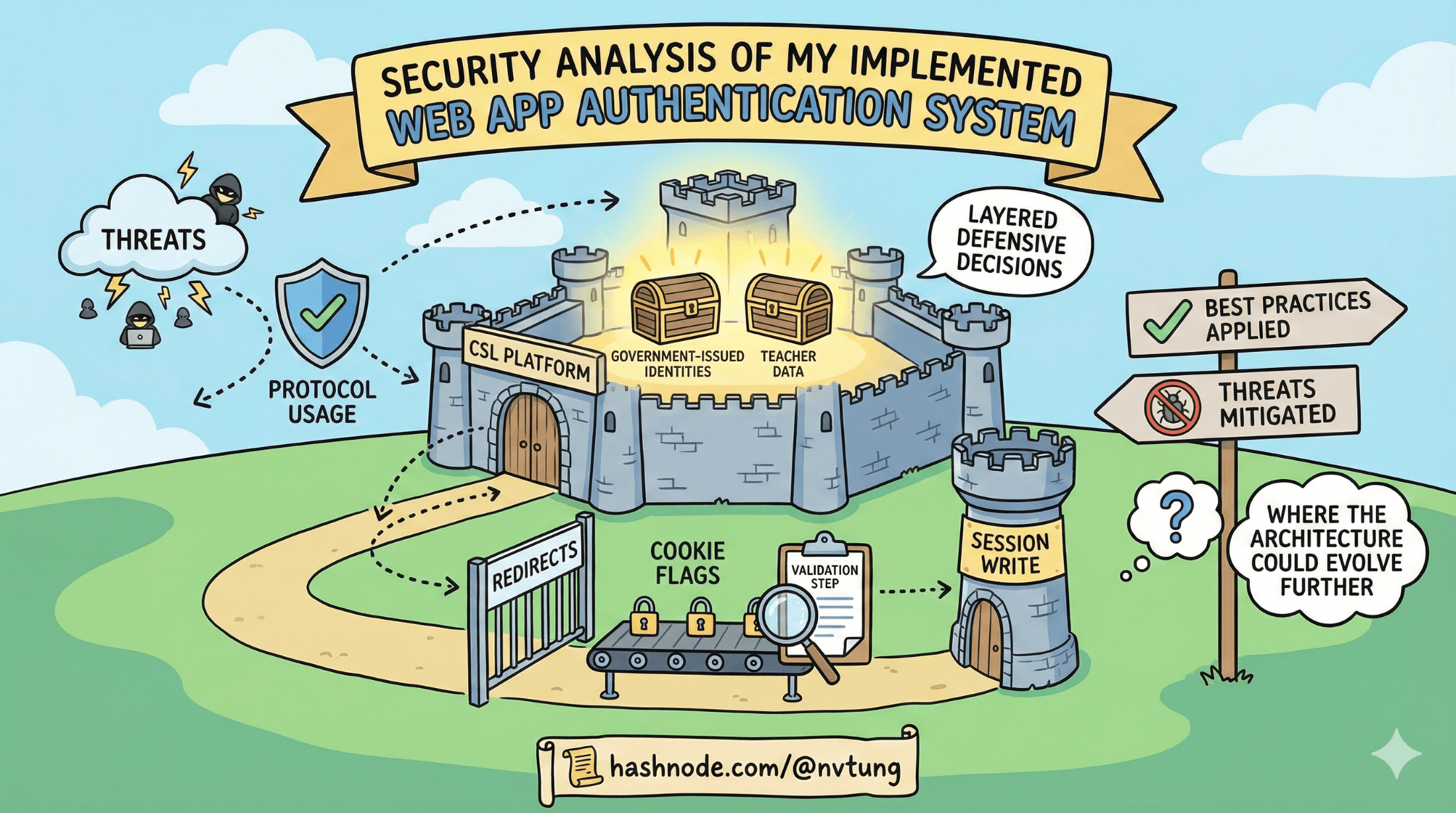
Security Analysis of my implemented Web App Authentication System
A detailed look at the security mechanisms behind the authentication flow—how threats are mitigated, tokens are validated, and sessions are protected
Search for a command to run...
Articles tagged with #infosec
A detailed look at the security mechanisms behind the authentication flow—how threats are mitigated, tokens are validated, and sessions are protected
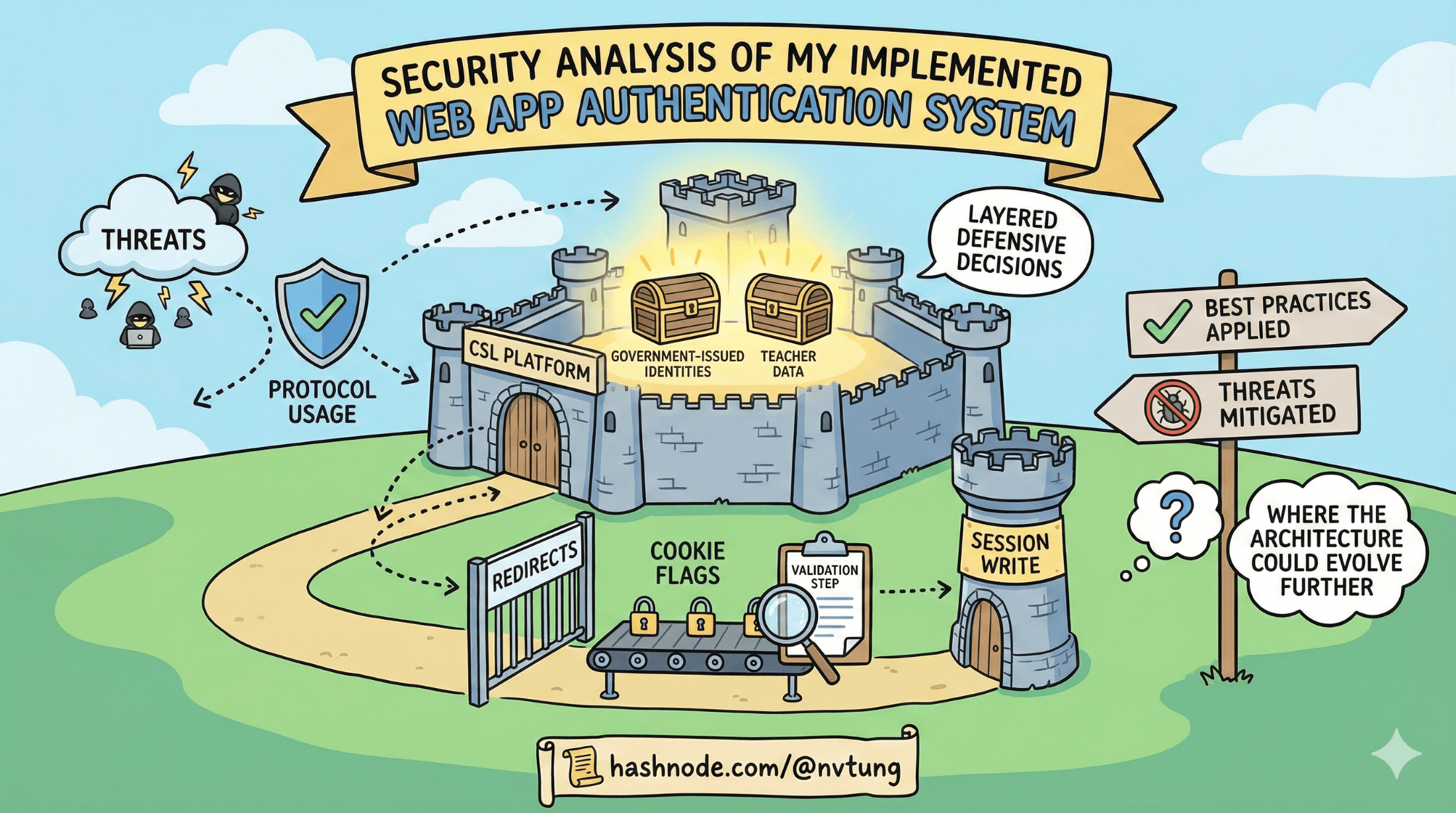
A step-by-step walkthrough of how the browser, IdP, Redis, HumHub, and CloudFront work together to authenticate a user in a real production system.
A high-level walkthrough of how the CSL web app authenticates users through a hybrid IdP + server-session design

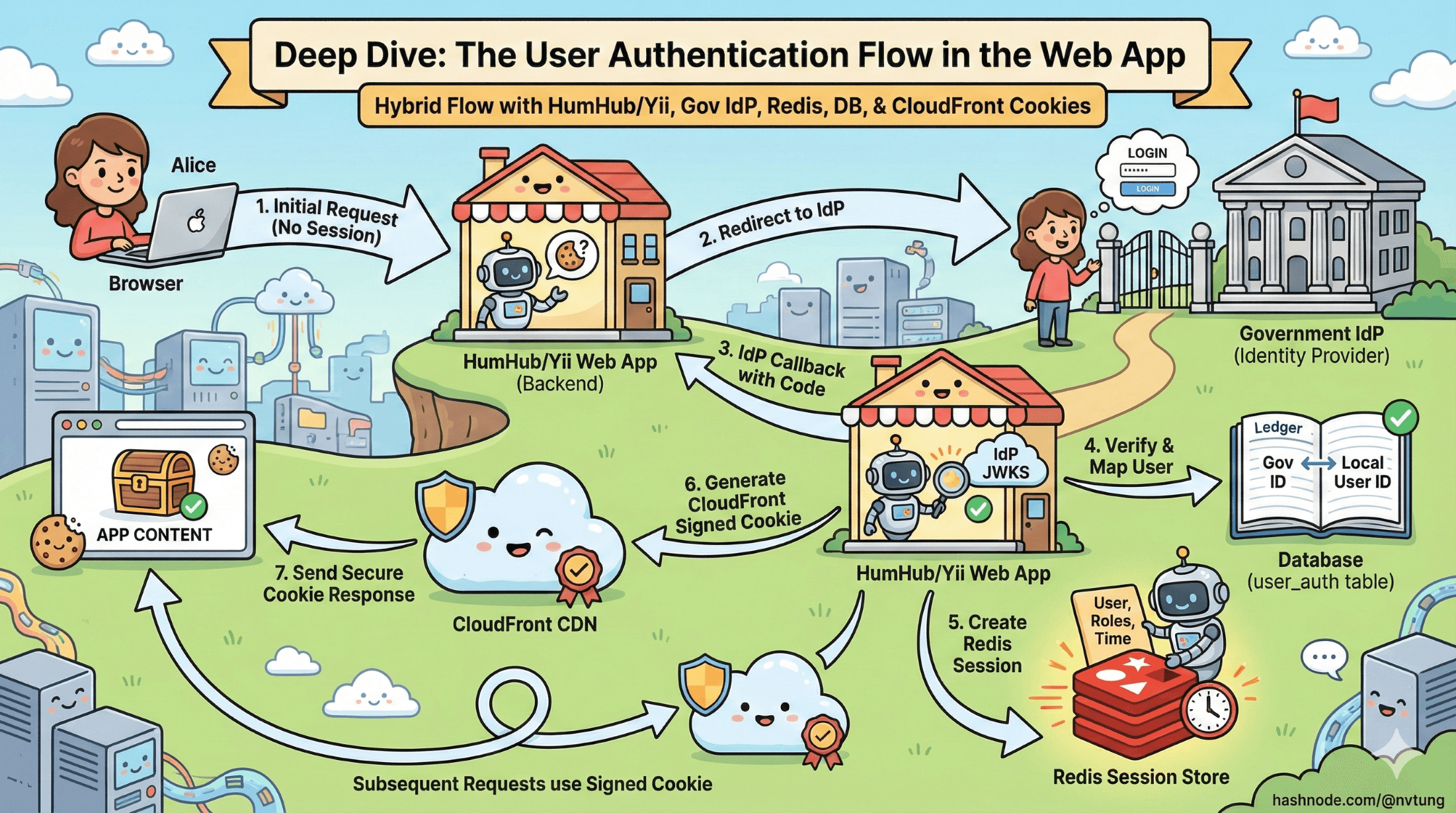
A practical look at how stateful sessions, stateless tokens, and hybrid models work—and how they shape real-world authentication.

A practical guide to understanding OAuth2 and OIDC flows—and how to choose the right one for your app.
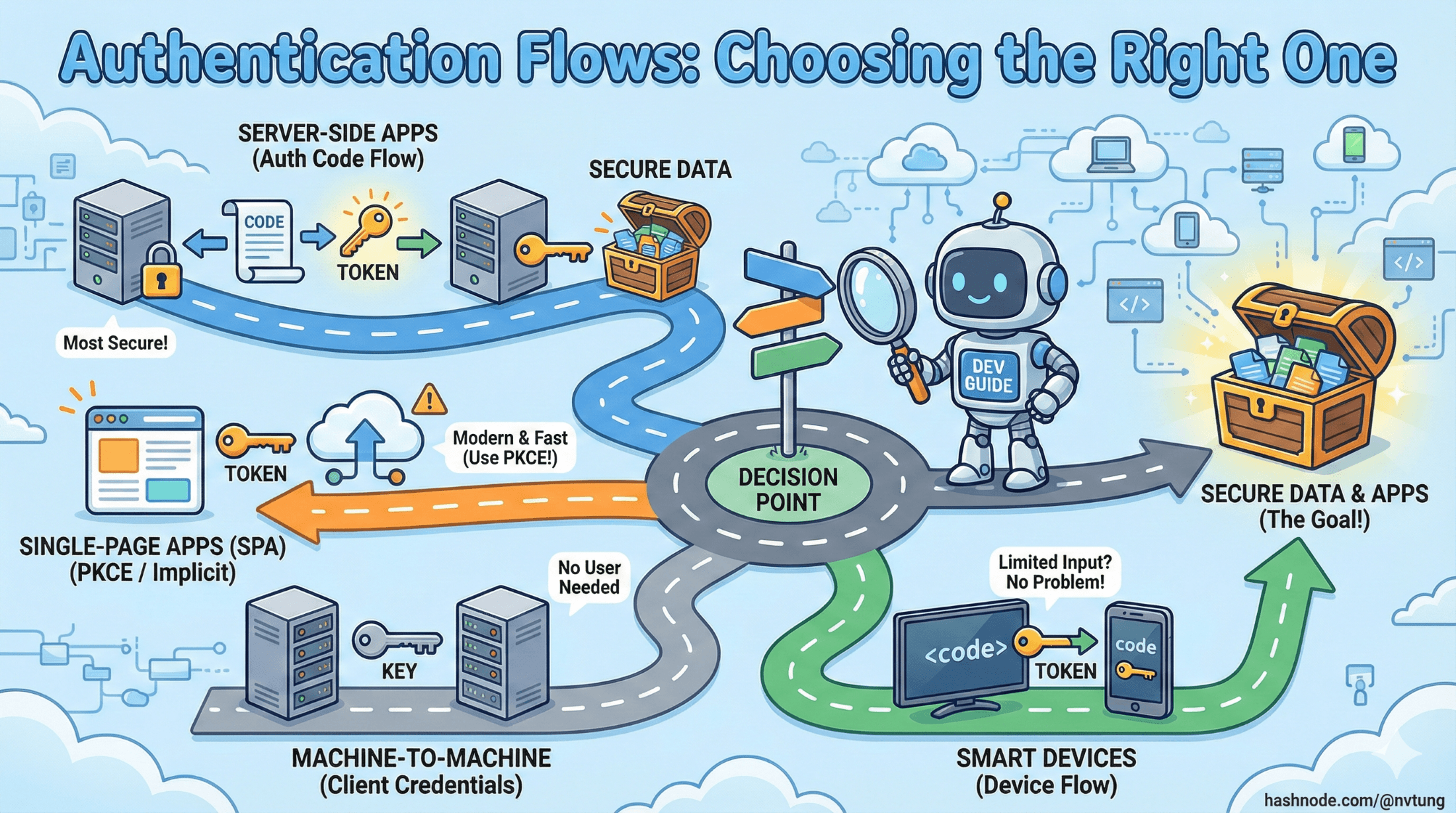
A clear guide to how OAuth2 and OIDC work together to provide modern authentication and secure delegated access.
